What Melee Gave Me
On or around November 19th, 2020, The Big House - one of the largest and storied tournaments for Super Smash Bros. Melee - received an unfortunate cease and desist notice from Nintendo of America, Inc.
Referenced in the matter is Slippi, a fan made, and supported, method of playing Melee online utilizing rollback, providing an almost console-level experience when it comes to netplay latency. In a year full of unpredictable events, and the worst pandemic of our lifetimes, Slippi has been vital in ensuring the health of the Melee scene without risking the health of individuals.
I'm not a lawyer, nor do I know the specifics of the cease and desist that The Big House received, so I can't comment on that. However, I wish Nintendo would reconsider their stance - I've been playing Melee since launch day, and it's meant the world to me, so I think it's worth sharing this.
For full disclosure, I've contributed to the Slippi project over the past few months - primarily on the Mac side of things, helping to ensure things work well there. I do it mostly because it feels like giving back to a game and community that gave me what you'll read below. With that said: none of the opinions in this post should be taken as representative of the Slippi team at all, though - mine, and mine alone.
Melee and Me
Super Smash Bros. Melee was released on Dec 3rd, 2001. I got my Gamecube shortly after, and with it, a copy of Melee. While I'd been playing fighting games for as long as I could remember (going all the way back to Street Fighter 2, then moving into the era of Third Strike, Marvel vs Street Fighter/Capcom, and so on - along with the requisite Smash 64 experience), this game immediately felt different. Not necessarily better, but expressive in a way they weren't - from graphics, to sound design, to movement options, to stage design and more, I was enthralled in a way no game had managed before.
I come from a rather large family (I'm the oldest of 7...), so we always had enough people to play with. We started, like many, with your standard Free-For-All matches on Hyrule Temple, moving on to trying every item option possible, exhausting the single player modes, and finding every trophy. At a certain point, the game felt complete... but fighting games have a competitive aspect to them, and there's always someone to try and beat.
So I found the competitive scene, and dabbled on and off. In the interest of keeping this readable, we're going to skip ahead a bit - just know that Melee was there for some of the most difficult and formative periods of my life.
Melee and Jamss
My youngest brother, Jake (or as he was known online, @notjamss), first found Melee by chance: walking through the living room while I was watching a tournament, and asking what it was. So we hung out there, and I started to explain the game, from tournament lore, to techniques and more. He was hooked - and wrote about it once, if you wanted his take.
Our family is from Northern Virginia, so it was perhaps natural that we'd want to attend SmashCon. We first went in 2016; for Jake, it was his first exposure to the competitive scene in real life, and we made plans to attend again. We missed 2017 due to my travel schedule, but we did hit 2018... albeit under some tougher circumstances.
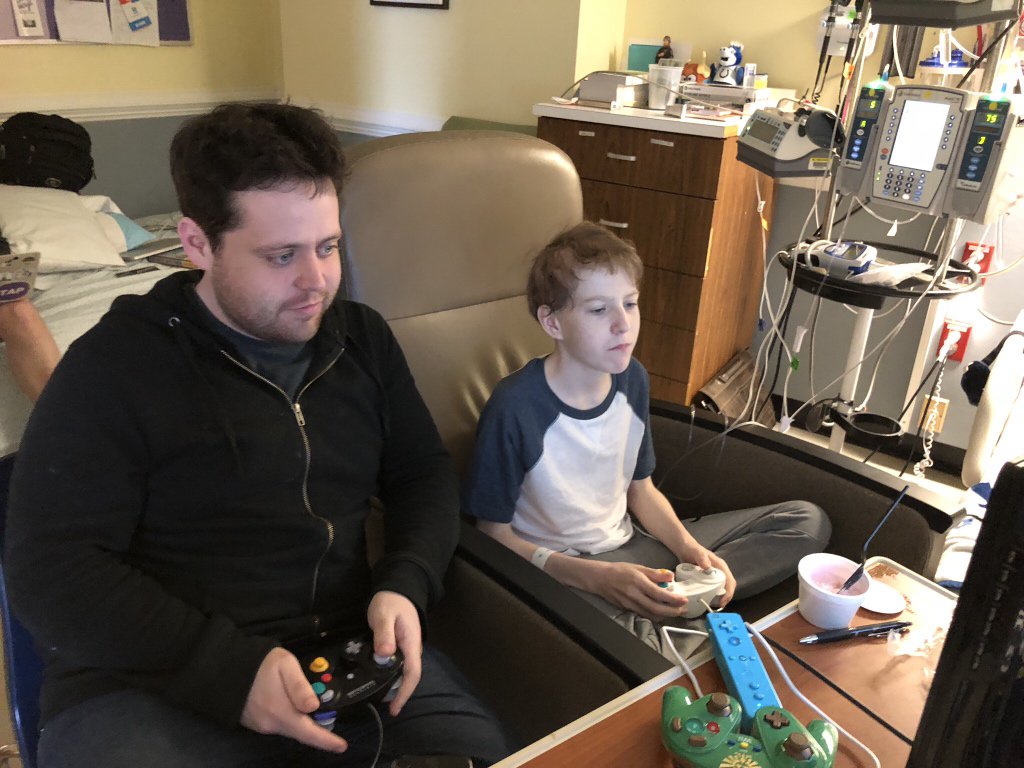
You see, in February of 2018, Jake was diagnosed with a combination of Acute Myleoid and Acute Lymphoid Leukemia. This required an immediate, and ultimately long, stay in the hospital. Our Father was (literally) always there with him, but the rest of us siblings would take turns staying with him. His room was almost amusing, considering everything we moved in there to make it better for him - including, most importantly, a working Melee setup.
And so play Melee, we did. A ton.
The Community
In an attempt to keep his spirits up in the hospital, I decided to see if I could put together some surprises for him. Through a friend of my lovely wife, we got Twitch to send him a care package. He had a fledgling interest in coding, so I sat with him and we put together a basic Smash.gg app, which wound up bringing a swag package from them as well. He'd alternate Twitch and Smash.gg hoodies for his walks around the hospital, and always seemed happy to explain them to anyone curious.
Most notably, though, was reaching out to Panda Global, who sent him a jersey that he could be found wearing... pretty much every day.

Graciously, they also said they'd be happy to meet and play with him if SmashCon 2018 was able to work out. I didn't tell Jake this, but I did tell him that if he made it out of the hospital by SmashCon I'd be happy to take him. His doctors worked tirelessly - and amazingly, he was able to go to outpatient treatment, albeit wearing a mask all the time (before it was popular).
The timing was tight, but I flew back, and off to SmashCon we went.
SmashCon 2018
Much has been written about this tournament elsewhere, and I encourage you to read (or watch!) it if you haven't: pretty much every game had fun sets and great Grand Finals, coupled with SmashCon's generally great setup for chilling and playing.
 Jake and I spent our time roaming around, playing various games and browsing the merchandise stalls. Jake got to meet up with some members of the community he'd been friends with for a bit, and the Panda Global crew made him feel like a VIP - MVD and Wobbles (Panda Global players at the time) in particular were great, with MVD somehow finding Jake in the crowd and welcoming him personally. Wobbles welcomed Jake into some friendlies and spent time showing him tech, and signed his new controller to replace the one from 2016.
Jake and I spent our time roaming around, playing various games and browsing the merchandise stalls. Jake got to meet up with some members of the community he'd been friends with for a bit, and the Panda Global crew made him feel like a VIP - MVD and Wobbles (Panda Global players at the time) in particular were great, with MVD somehow finding Jake in the crowd and welcoming him personally. Wobbles welcomed Jake into some friendlies and spent time showing him tech, and signed his new controller to replace the one from 2016.
A very friendly Panda Global representative, who I've unfortunately forgotten the name of, eventually found us and asked Jake if he'd like to meet Plup and play some games with him. Jake jumped at the chance, and they played for about an hour or so. If I recall correctly, Plup wasn't feeling the best, but still went out of his way to do this - and it meant a lot to Jake.

To top it all off, we watched what is one of the greatest Grand Finals set of all time (and the final US singles set before Armada's sudden retirement). Here, Melee gave me one of the best weekends of my life.
 We left SmashCon 2018 feeling great, and we'd continue our general tournament watching and netplay sessions. Since I was located in Seattle, this became our way of staying close even when I couldn't hang with him in-person.
We left SmashCon 2018 feeling great, and we'd continue our general tournament watching and netplay sessions. Since I was located in Seattle, this became our way of staying close even when I couldn't hang with him in-person.
Eventually, Jake made it to a stable enough place to go for a bone marrow transplant (and thankfully, one other sibling was a good match). He got it, and we waited to see if it worked.
Saying Goodbye
Unfortunately, science just sucks sometimes. The doctors did everything they could, but it looked as if it just wasn't taking - Jake's cancer was pretty rare, and options became limited to comfort to ride it out. Jake would ultimately pass at home, surrounded by family and without pain. We miss him every day.
For me, I've struggled to write about this experience since it happened, and it's the subject of another blog post that I'll eventually finish writing, when the words come. What I wanted to showcase here, though, happened shortly before Jake passed.
Before death, some experience what's known as a "surge" or "rally" - a noticeable, but short, return to energy and form. It can be jarring to witness, mostly due to the juxtaposition of watching the decline beforehand - but in a way, it's beautiful too. Jake had a rally, and he looked up, and asked if we wanted to play Melee.
We all kind of just looked around, and then said yes. We played a few one on one, and then we swapped out and played group games with the cast of siblings.

To this day, they were the most surreal games of Melee I've ever played.
Some quick additional context might explain. Fighting games in general (and Melee in particular) are incredibly complex games, and Melee served as a great test for eyeing decline. When we'd play in the hospital, or over netplay, Jake and I would often ask each other if his reactions started to get slower, or if the game became difficult to play - for example, hands not listening, or being unable to process things on screen. Against the odds (and likely thanks to the support of his incredible doctors), he never really declined.
Except towards the end of those last games.
Jake had never really talked much about the concept of death, other than being proud that any research or efforts on his condition might be helpful to others down the road. I spent a few months struggling to parse these games, until one day I realized that Melee had transcended just being a game for us - it was a language, and that was our goodbye. We were given closure in a package I didn't understand, but to this day I'm thankful for it.
On Melee
This post leans heavily personal, and I'd forgive anybody for wondering how this pertains to the Big House Online cease and desist.
Simply put: I wanted to showcase what Melee gave me. The game is approaching 20 years old, and while I understand Nintendo wanting to protect copyright and trademark and so on, there comes a time where, like any child, it ceases to just be a product of your own creation.
Melee as an experience is defined by the 20 year rollercoaster of a community it developed. There is no other Smash Bros. game that has reached the level that Melee has, and there is no technological achievement, or cast of characters, or quirky mechanics that can match it - because Nintendo, frankly, did not create the part of Melee that matters now. But they could be a part of it.
Nintendo, if you happen to read this: I get that you're the "family friendly" company, and I understand you're a business. But families come in different shapes and sizes, and Melee meant more to mine than you could possibly imagine.
I implore you to reconsider your position, and find a way to get okay with streaming tournaments.